How to configure passwordless SSH login
Passwordless SSH login removes repeated remote account password prompts from routine administration, remote commands, and file transfers. Once the key is trusted on the server, the same account can be reached quickly for day-to-day work and automation that still needs normal SSH access.
In a typical OpenSSH setup, the private key stays on the local machine and the matching public key is appended to the remote user's ~/.ssh/authorized_keys file. During login, the client proves possession of the private key and sshd accepts the session when public-key authentication is enabled for that account.
The first key install usually still needs one successful login with the remote account password or another working sign-in method because ssh-copy-id connects over SSH to add the key. A passphrase on the private key can still trigger a local prompt unless the key is already loaded into ssh-agent, and the first connection to a new host may also ask to confirm the server host key.
Steps to configure passwordless SSH login:
- Generate an Ed25519 key pair on the local machine if the account does not already have one.
$ ssh-keygen -t ed25519 Generating public/private ed25519 key pair. Enter file in which to save the key (/home/user/.ssh/id_ed25519): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/user/.ssh/id_ed25519 Your public key has been saved in /home/user/.ssh/id_ed25519.pub
Press Enter at the file prompt to keep the default ~/.ssh/id_ed25519 path so ssh can find the key automatically later.
If the file already exists, keep the current key or choose a different filename instead of overwriting an active identity.
Leaving the passphrase empty is best reserved for tightly controlled automation. For normal interactive access, a passphrase or ssh-agent is the safer default.
- Install the matching public key on the remote account with ssh-copy-id.
$ ssh-copy-id -i ~/.ssh/id_ed25519.pub user@host.example.net /usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/home/user/.ssh/id_ed25519.pub" /usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed /usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys Number of key(s) added: 1 Now try logging into the machine, with: "ssh 'user@host.example.net'" and check to make sure that only the key(s) you wanted were added.
The first run normally prompts once for the remote account password so the public key can be appended to ~/.ssh/authorized_keys.
ssh-copy-id creates the remote .ssh directory and authorized_keys file if they do not already exist.
Use -p 2222 or another port number if the server does not listen on the default SSH port.
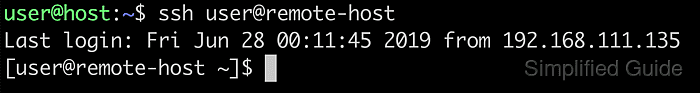
- Open a new session and confirm that the remote account no longer asks for its password.
$ ssh user@host.example.net 'whoami' user
A prompt for the private-key passphrase is local to the client and is separate from the remote account password. Load the key into ssh-agent if repeated local passphrase prompts are not wanted.
If the remote account password prompt still appears, the server did not accept the key yet. Re-copy the correct public key or confirm that public-key logins are still enabled on the server.