Public-key authentication in SSH enables access to remote accounts using a cryptographic key pair instead of a password, reducing exposure to brute-force attacks and avoiding repeated credential prompts during daily administration or automation.
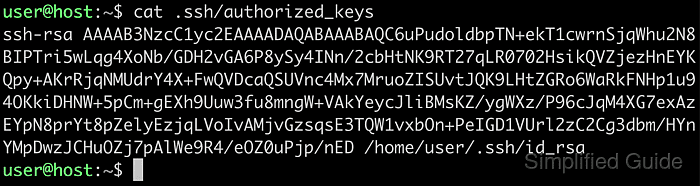
In a typical OpenSSH setup, the public key resides in the local ~/.ssh directory with a .pub extension, while the private key stays on the local machine. The remote server reads the user's ~/.ssh/authorized_keys file during connection setup and grants access when a key listed there matches the private key offered by the client.
Reliable key-based login assumes an existing key pair, a reachable remote account, and correct permissions on the ~/.ssh directory and authorized_keys file. Using the ssh-copy-id helper preserves file format and permissions automatically, avoiding common problems such as malformed key lines or permission errors that cause OpenSSH to ignore keys.
Steps to copy SSH public key to server using ssh-copy-id:
- Open the terminal on the local machine.
- Locate the SSH public key in the ~/.ssh directory.
$ ls ~/.ssh/id* /home/user/.ssh/id_ed25519 /home/user/.ssh/id_ed25519.pub
The public key normally has the .pub extension.
- Verify that the key is in the OpenSSH public key format.
$ file ~/.ssh/id_ed25519.pub /home/user/.ssh/id_ed25519.pub: OpenSSH ED25519 public key
The authorized_keys file accepts public keys in OpenSSH format only.
- Use the ssh-copy-id command to add the public key to the remote server account.
$ ssh-copy-id user@host.example.net /usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/home/user/.ssh/id_ed25519.pub" /usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed /usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys Number of key(s) added: 1 Now try logging into the machine, with: "ssh 'user@host.example.net'" and check to make sure that only the key(s) you wanted were added.
To use a different public key file instead of the default, specify it with the -i option.
$ ssh-copy-id -i ~/.ssh/other_key.pub user@host.example.net
- Test the connection to the server using the SSH key.
$ ssh -i ~/.ssh/id_ed25519 user@host.example.net 'hostname' host
Alternative methods:
- Manually append the local public key from ~/.ssh/id_ed25519.pub to the remote server's ~/.ssh/authorized_keys file using a text editor or file transfer.
- Pipe the public key directly into the remote authorized_keys file.
$ cat ~/.ssh/id_ed25519.pub | ssh user@host.example.net 'cat >> ~/.ssh/authorized_keys'
Editing or overwriting entries in ~/.ssh/authorized_keys incorrectly can prevent other keys from authenticating or remove existing access for users.

Mohd Shakir Zakaria is a cloud architect with deep roots in software development and open-source advocacy. Certified in AWS, Red Hat, VMware, ITIL, and Linux, he specializes in designing and managing robust cloud and on-premises infrastructures.
