Routing SSH connections through a jump host, also known as a bastion host, concentrates external access on a single hardened entry point while keeping internal servers on private addresses. Using a dedicated gateway limits exposed services and simplifies firewall rules for segmented networks.
In OpenSSH, the ProxyJump (-J) option instructs the client to first establish an SSH connection to the jump host and then automatically create a TCP tunnel to the final destination. This replaces manual multi-hop login sequences with a single command or configuration stanza, while still using standard public key or password authentication on each hop.
Correct configuration depends on a client that supports ProxyJump (OpenSSH 7.3 or newer), reachable network paths between the gateway and internal hosts, and appropriate forwarding permissions on the jump server. Misconfigured settings may cause authentication loops or timeouts, so a working manual login path is important before switching to automated jump host configuration.
Steps to connect to an SSH server through a jump host:
- Open a terminal on the external host that can reach the jump host over the network.
- Verify SSH access from the external host to the jump host and from the jump host to the internal server.
$ ssh user@gateway hostname host $ ssh user@internal -p 2222 hostname host
- Use the ProxyJump option to connect to the internal server through the jump host with a single SSH command.
$ ssh -J user@gateway user@internal -p 2222 hostname host
Use comma-separated values in -J when multiple jump hosts are needed.
$ ssh -J user@gateway,user@gateway2 user@internal
Add :port to a jump host entry in -J when the SSH service listens on a non-standard port.
$ ssh -J user@gateway:2222 user@internal
-J destination Connect to the target host by first making a ssh connection to the jump host described by destination and then establishing a TCP forwarding to the ultimate destination from there. Multiple jump hops may be specified separated by comma characters. This is a shortcut to specify a ProxyJump configuration directive. Note that configuration directives supplied on the command-line generally apply to the destination host and not any specified jump hosts. Use ~/.ssh/config to specify configuration for jump hosts.Set AllowAgentForwarding and AllowTcpForwarding to yes on the jump server when using SSH agent forwarding or public key authentication through the gateway.
Requires OpenSSH 7.3 or newer on the client; older versions do not support ProxyJump and must use ProxyCommand instead.
- Open the SSH user configuration file in a text editor.
$ vi ~/.ssh/config
- Add a named host entry for the jump host in the configuration file.
Host gateway HostName gateway User user
- Add the internal server definition and reference the jump host using ProxyJump.
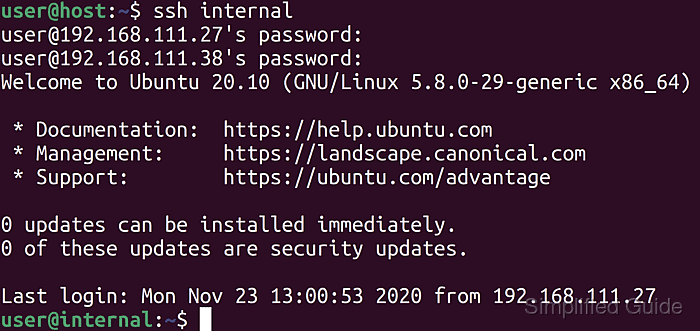
Host internal HostName internal User user Port 2222 ProxyJump gateway
- Save the configuration changes in the editor.
- Connect directly to the internal server using its host alias to confirm that the jump configuration works.
$ ssh internal hostname host
Mohd Shakir Zakaria is a cloud architect with deep roots in software development and open-source advocacy. Certified in AWS, Red Hat, VMware, ITIL, and Linux, he specializes in designing and managing robust cloud and on-premises infrastructures.
