Public access to an SSH tunnel allows applications and users on other hosts to reuse a single encrypted connection for web browsing, diagnostics, or access to internal services. Binding the tunnel to an external IP address turns a local-only endpoint into a shared resource on the network.
In OpenSSH, local and dynamic port forwarding options such as ssh -L and ssh -D create listening sockets on the client side and forward traffic over the secure channel to the remote server. By default these sockets bind to 127.0.0.1, but a custom listening address and the -g option can expose the same tunnel on another local interface, making it reachable from remote hosts on that network segment.
Allowing remote hosts to reach a tunnel effectively publishes a proxy or forwarded service, which can open a path for abuse if left unprotected. Firewall rules, access control lists, and careful choice of listening address (for example, a private LAN interface instead of 0.0.0.0) limit exposure while still enabling the required access. Changes should be tested from a known-safe network and reviewed regularly to ensure the tunnel does not become an unintended open proxy on the internet.
Related: How to forward local port in SSH
Related: How to disable SSH TCP forwarding
Steps to enable public access to SSH tunnel:
- Identify the external IP address of the host running the tunnel.
$ ip -4 addr show enp0s5 2: enp0s5: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000 inet 203.0.113.50/24 brd 203.0.113.255 scope global dynamic noprefixroute enp0s5 valid_lft 1072sec preferred_lft 1072sec - Create an SSH dynamic port-forward tunnel that listens on this external IP address.
$ ssh -fN -g -D 203.0.113.50:8080 user@host.example.net
Related: How to create an SSH SOCKS proxy
Exposing a public SOCKS proxy can be abused as an open proxy; restrict access to trusted networks and addresses.
- Verify that the tunnel is active and listening on the specified IP.
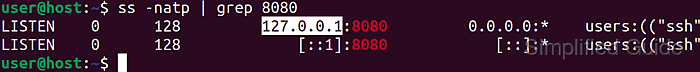
$ ss -natp | grep 8080 LISTEN 0 128 203.0.113.50:8080 0.0.0.0:* users:(("ssh",pid=14690,fd=4)) - Configure the firewall to allow incoming connections to the tunnel port if a firewall is enabled.
$ sudo ufw allow 8080 # Ubuntu and Debian variance $ sudo firewall-cmd --zone=public --permanent --add-port=8080/tcp # CentOS and Red Hat variance $ sudo firewall-cmd --reload # CentOS and Red Hat variance
UFW manages host-based firewall rules on Ubuntu and Debian, while firewalld with firewall-cmd is common on CentOS and Red Hat Enterprise Linux.
- Test access to the tunnel from a remote host to confirm connectivity.
$ curl --proxy socks5://203.0.113.50:8080 https://ifconfig.me 203.0.113.50

Mohd Shakir Zakaria is a cloud architect with deep roots in software development and open-source advocacy. Certified in AWS, Red Hat, VMware, ITIL, and Linux, he specializes in designing and managing robust cloud and on-premises infrastructures.
