Controlling whether the root account can log in directly over SSH reduces exposure of the most privileged user on a server. Disabling direct root access forces administration through unprivileged accounts that escalate with sudo, limiting the impact of password guessing and credential theft.
On typical Linux systems, the OpenSSH server process sshd reads its configuration from /etc/ssh/sshd_config during startup. The PermitRootLogin directive in this file determines if logins for the root user are accepted, rejected entirely, or restricted to specific methods such as public-key authentication or forced commands.
Changes to /etc/ssh/sshd_config affect every incoming SSH session and invalid settings can prevent sshd from starting. Before disabling root login, at least one non-root account with SSH and sudo access is required to avoid losing remote administrative access. The steps below assume OpenSSH managed by systemd on a modern Linux distribution and focus on adjusting PermitRootLogin safely.
Related: How to allow or deny SSH access for users and groups
Related: How to allow or disallow SSH password authentication
Make sure a non-root user with SSH and preferably sudo access exists before preventing root access.
Steps to deny or allow root login in SSH:
- Confirm availability of a standard user account with SSH and sudo access.
- Open a terminal session with access to the target server.
- Edit the /etc/ssh/sshd_config file as a privileged user.
$ sudo vi /etc/ssh/sshd_config [sudo] password for user:
- Locate the PermitRootLogin directive or add it if it is missing.
Add the line if it does not already exist and remove any leading # character to uncomment it.
- Set PermitRootLogin to the desired value for enabling or disabling direct root login.
PermitRootLogin no
PermitRootLogin
Specifies whether root can log in using ssh(1). Supported values are yes, prohibit-password, forced-commands-only, and no; the default is prohibit-password. - Save the configuration file and exit the editor.
- Validate the sshd configuration syntax before restarting the service.
$ sudo sshd -t
No output indicates that the configuration syntax is valid.
Related: How to test SSH server configuration
- Restart the SSH daemon to apply the configuration change.
$ sudo systemctl restart ssh
- Verify that the sshd service is running after the restart.
$ sudo systemctl status ssh ● ssh.service - OpenBSD Secure Shell server Loaded: loaded (/usr/lib/systemd/system/ssh.service; enabled; preset: enabled) Active: active (running) since Sat 2026-01-10 20:02:28 +08; 4min 7s ago TriggeredBy: ● ssh.socket Docs: man:sshd(8) man:sshd_config(5) Process: 13689 ExecStartPre=/usr/sbin/sshd -t (code=exited, status=0/SUCCESS) Main PID: 13694 (sshd) Tasks: 1 (limit: 4546) Memory: 2.7M (peak: 5.2M) CPU: 231ms CGroup: /system.slice/ssh.service ##### snipped #####
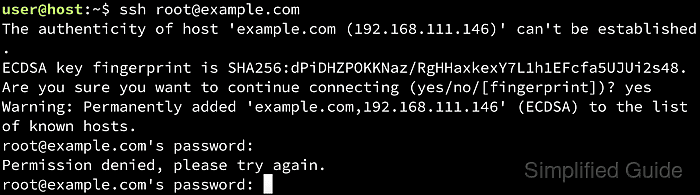
- Test root login behavior from a separate session to confirm that the configured policy is in effect.
$ ssh -o BatchMode=yes root@host.example.net root@host.example.net: Permission denied (publickey,password).
A repeated Permission denied prompt for root confirms that PermitRootLogin no is being enforced.

Mohd Shakir Zakaria is a cloud architect with deep roots in software development and open-source advocacy. Certified in AWS, Red Hat, VMware, ITIL, and Linux, he specializes in designing and managing robust cloud and on-premises infrastructures.
