How to configure multiple AWS CLI profiles
Configuring separate named profiles in AWS CLI keeps staging, production, audit, and personal access from sharing one fallback credential path. That matters on admin workstations, support shells, and automation hosts where the next command must land in the intended AWS account.

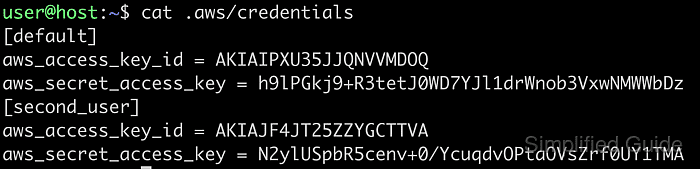
Named profiles store credentials in ~/.aws/credentials and profile defaults such as region and output in ~/.aws/config. The [default] profile is only the unnamed fallback when no other profile is selected, and current AWS documentation states that named profiles do not inherit values from [default] automatically.
Running aws configure --profile profile-name writes an access-key-backed named profile for that account or environment. If the target uses IAM Identity Center or an assumed role instead of long-lived keys, create that profile with its own flow first and then use the same selection and verification steps shown here.
Related: How to switch AWS CLI profiles
Related: How to use AWS CLI environment variables
Steps to configure multiple AWS CLI profiles:
- Create the first named profile with the interactive wizard and enter the access key, secret key, default Region, and output format for that account.
$ aws configure --profile engineering Tip: You can deliver temporary credentials to the AWS CLI using your AWS Console session by running the command 'aws login'. AWS Access Key ID [None]: AKIAIOSFODNN7EXAMPLE AWS Secret Access Key [None]: wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY Default region name [None]: us-west-2 Default output format [None]: json
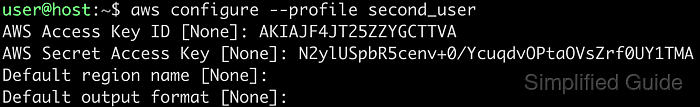
Use a profile name that matches the workload, such as engineering, production, billing, or audit, so later --profile selections stay readable.
- Repeat the same command for each additional account or environment that needs its own saved defaults.
$ aws configure --profile production Tip: You can deliver temporary credentials to the AWS CLI using your AWS Console session by running the command 'aws login'. AWS Access Key ID [None]: AKIAIOSFODNN7EXAMPLE AWS Secret Access Key [None]: wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY Default region name [None]: us-east-1 Default output format [None]: yaml
Create IAM Identity Center profiles with How to log in to AWS CLI with IAM Identity Center and assumed-role profiles with How to assume an IAM role using AWS CLI instead of reusing long-lived key pairs for those flows.
- List the saved profile names and confirm the expected set is present before using any of them.
$ aws configure list-profiles engineering production
If the shared files already contain a [default] profile, it appears as default in this list beside the named profiles.
- Inspect one named profile and confirm that the Region and credential source resolve from the shared files.
$ aws configure list --profile production NAME : VALUE : TYPE : LOCATION profile : production : manual : --profile access_key : ****************MPLE : shared-credentials-file : secret_key : ****************EKEY : shared-credentials-file : region : us-east-1 : config-file : ~/.aws/config
The TYPE and LOCATION columns show whether the values came from the named profile files instead of from exported shell variables.
- Run a low-risk identity check with the named profile before any command that changes live resources.
$ aws sts get-caller-identity --profile production --query Account --output text 210987654321
The returned account ID should match the intended environment before deployments, data copy jobs, or permission changes continue.
Related: How to check the current caller identity in AWS CLI - Export AWS_PROFILE when several commands in the same shell should stay on one named profile.
$ export AWS_PROFILE=engineering
Clear AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY, and AWS_SESSION_TOKEN first if they are already exported, because those variables override the credentials that the named profile would otherwise supply.
- Check the resolved shell defaults after exporting the profile.
$ aws configure list NAME : VALUE : TYPE : LOCATION profile : engineering : env : ['AWS_PROFILE', 'AWS_DEFAULT_PROFILE'] access_key : ****************MPLE : shared-credentials-file : secret_key : ****************EKEY : shared-credentials-file : region : us-west-2 : config-file : ~/.aws/config

The profile row should show env from ['AWS_PROFILE', 'AWS_DEFAULT_PROFILE'], while an explicit --profile on a later command still overrides the shell default for that one request.
- Clear the shell-level profile override when the session should stop using the temporary shell default.
$ unset AWS_PROFILE
Removing the override prevents later commands, tabs, or pasted shell snippets from continuing to use the previous account by mistake.